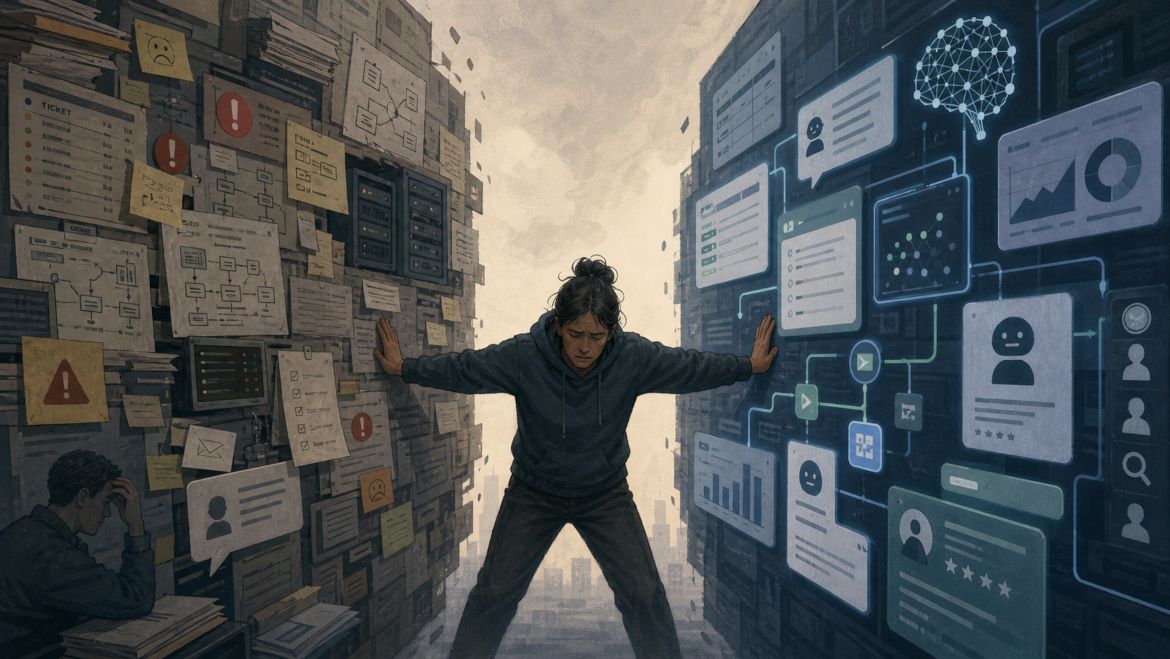
‘Are cyber jobs being stretched to breaking point by AI?’ – A blog by IoTSF member You Gotta Hack That
"How much change can one tired person metabolise before we stop calling it resilience, or strength, and start calling it what it is? Because that seems like a big chunk of the AI conversation that we all keep politely stepping around."