IoTSF founder member ElevenPaths have just released a trend report titled
IoTSF founder member ElevenPaths have just released a trend report titled
“Insecurity in the Internet of Things”
The report is freely downloadable from HERE
“Security lessons of the past 20 years have often been forgotten by existing technology vendors”
Executive Summary
enterprise the IoT is seen as an integral part of the blueprint for developing from the digital business
model of today to the digitisation of the entire value chain, and in the consumer space ‘wearable’
adoption is rising rapidly. However significant advances in edge computing, networks, big data and
analytics are still required for this truly disruptive technology to shape the future; and widespread
implementation is likely to be 5-10 years away.
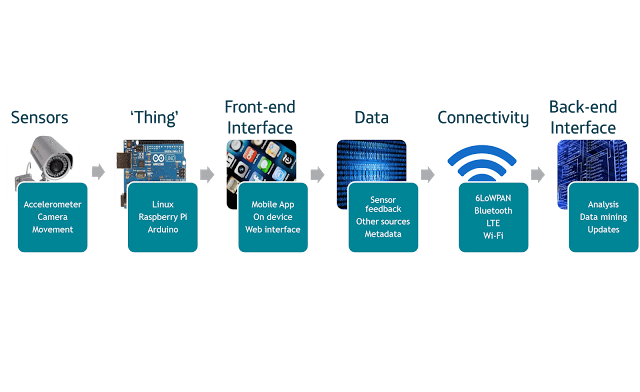
Such scope ensures that IoT should not be thought of as just a ‘Thing’ in itself; it is a collection of
technologies integrated and presented to provide specific and vastly diverse applications. At this nascent
stage in the lifecycle, focus on securing it can be disproportionately weighted on the end device,
forgetting that it is merely a component of a larger eco-system that is only as strong as its weakest link.
Aside from the inherent restrictions on security measures due to size and cost of many devices, the
quantity and nature of data to be collected and transmitted, and tackling user behavioural traits also
provide complex challenges.
Methods to subvert these technologies will depend both on the manner in which they mature, and how
security is implemented on often exposed devices. Worryingly, the early indications are that the network,
application and cloud security lessons of the past 20 years have often been forgotten by existing
technology vendors, and not yet learnt by manufacturers pushing into a new market.
While risk exposure from IoT vectors is likely to remain low in the short term for most enterprises, it may
be higher than first thought. Some risks will undoubtedly become more relevant as the IoT ecosystem
matures; fraudulent use of IoT based services, or danger of physical harm through failure or
manipulation. Avoiding distraction from the future or edge cases, the uptick in reflective DDoS attacks
during H2 2014 already indicates one negative consequence of an insecure IoT. The natural extension of
shadow IT combined with confluence of home and office working means IoT devices may already be
permeating corporate networks, and the potential of almost permissionless innovation has the potential
to fundamentally change the way we look at data protection.
The concept of security by design must be given a higher priority in order to avoid security flaws being
compounded as the IoT matures, and adopters should be alert to IoT integration in a less mature, loosely
regulated environment, or risk costs spiralling later. Core principles of data, application, network, systems
and hardware security remain applicable but the complexity is higher and measures must be more careful
not to work against the user. The IoT will be transformational, disruptive technological movement, but
carries a spectrum of risks that affect more than just the IT department.