By John Moor, MD IoTSF
It’s hard for me to recall the first time I came across the term ‘the Internet of Things’, but it is likely to be circa 2005. I do remember thinking it quite vulgar – a load of bull, as my lingua franca of the day used terms such as ‘pervasive computing’ and ‘ubiquitous sensing’, you know, respectable professional engineering language. Terminology aside, up until 2015 I was truly inspired by the impact connected digital technologies were going to have on society – the quiet revolution was in full swing and innovation was my future world.
Then, just over 3 years ago, I started to look at IoT from a security perspective. To say it has been an insightful journey is quite the understatement. It’s not a focus I chose myself, I was motivated in that direction by a person of great influence. Nevertheless, I recall my initial thoughts of “isn’t cybersecurity a mature subject?” and wondered why I had been invited to take a look at, what appeared to be, an esoteric subject.
I’m smiling as I type this, as I have long since learned the ugly truth about IoT security (see Mike Muller’s talk in side bar). I can forgive myself for such naivety, having witnessed the same perception many times since, and by greater people. As happened with me, it usually doesn’t take too long to shift from the position of “what’s the problem?”, to a “wow, that’s a big problem that needs fixing”. In the days that have passed since, I have (figuratively) travelled to many places in the land of IoT, and I submit to you without hesitation that IoT insecurity is a wicked challenge for the real, physical world today. Nations, governments, society, industry, business, consumers and citizens, we are all implicated in the unfolding plot of good versus evil, and it will require significantly more than security expert heroes to address the issues.
[See also Take note: UK Government publishes its proposed Code of Practice for Security in Consumer IoT]
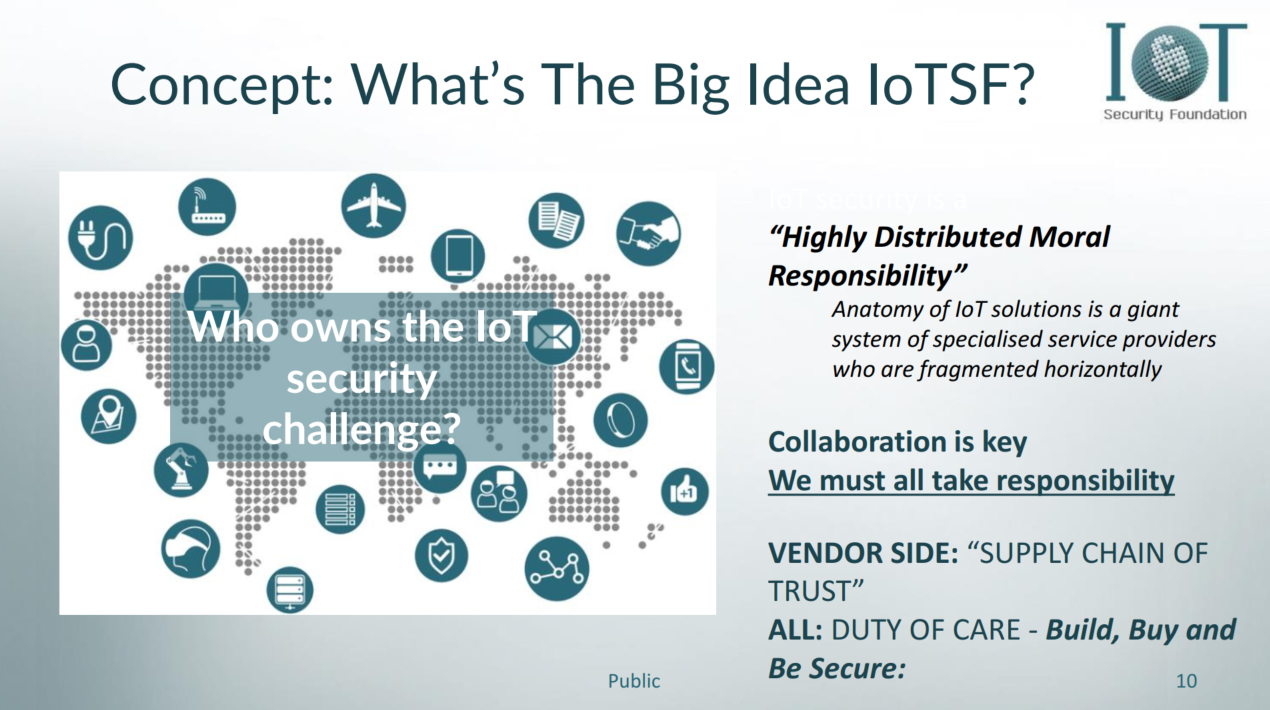
I use the term ‘address’ advisedly in preference to ‘solve’, as I discovered at the start of my journey that ‘perfect security is asymptotic’ – almost impossible to achieve as the target keeps moving. When you set this alongside other observations, such as ‘security does not compose’, and further consider it in relation to the complexity/interdependency of workings that IoT represents, you quickly recognize that many measures, applied across the IoT environment, and by many stakeholders, are necessary to manage the risk to an acceptable level. Defense in depth is where we find answers – we need to break the problem down so we can understand who needs to take responsibility, as well as where, and to what degree.
As we established the IoT Security Foundation, it was self-evident that the challenges were widespread, and impossible to work on them all at once. Hence our plan has been to simplify, prioritise and focus. In 2015, the consumer IoT space was of greatest concern – indeed, ‘egregious’ was a word I used daily. It was clear we needed to focus our attention on the consumer vendors, as many were taking short cuts or ignoring security entirely – ignorance and apathy were systemic.
To help get us moving, we encapsulated our founding values of ‘security first, fitness of purpose and resilience’ to effectively communicate:
1. Security needs to be by design, not an afterthought
2. Context is all, security measures are most effective when informed by the environment
3. Accept the probability that, despite your best efforts, you will get hacked. This means you will need to plan for your recovery and response processes – ahead of likely incidents.
Since that time, the IoTSF membership has collaborated to produce a number of best practice guides and a security framework for vendors. They’re written with a non-expert audience in mind, to help those who need it most move closer to market speed. The logic is simple; if security knowledge can be made consumable, and vendors encouraged to provision fit-for-purpose security capabilities more readily, consumers and businesses (ahem, Mirai) will be more secure.
As part of the consumer-prioritized vendor initiative, we also felt the need to provide greater context and spread awareness as to ‘who owns the IoT security challenge?’. I’ve spoken about this many times, and I use a term from an academic paper which characterizes it as a ‘highly distributed moral responsibility’ – in layman’s terms, ‘we all own the challenge’. For the supply chain, we have borrowed language from the security lexicon and devised the concept of a ‘supply chain of trust’ so that all supply chain actors understand they have a role to play – not just the final product builder.
And it does not stop there. Our story is extending to more stakeholders as we grow and build on what we have produced so far. We further need to start a conversation with retailers and purchasers as they have a key role to play in making sure the vendors do the right thing. Retailers can choose to not stock or sell products that could be weaponized against us due to the lack of basic security protections. And purchasers, significantly in government and business procurement departments, need to make sure they specify security requirements to their suppliers – and follow through by ensuring they meet the requirements. In this way we can increase the security assurance level throughout IoT.
It extends further, to the users. We are now firmly into the digital transformation and digital hygiene is no longer optional. Just as we teach our children basic physical hygiene, digital hygiene is now a fact of life.
Here comes the BS
Once again, we’ve tried to encapsulate simple, yet powerful, messaging to communicate to key stakeholders in our quest to address that wicked challenge of IoT insecurity and urge you, wherever you may be in IoT land, to Build Secure, Buy Secure and Be Secure – the 3 BS’s:
Build Secure – if you’re a vendor, make sure you provision security, by design
Buy Secure – if you’re buying connected products or services, make sure you specify security
Be Secure – if you’re a user, don’t be the weakest link, take care of the basics, make passwords hard to guess, update software and report suspicious activity.
That’s why IoT security needs more BS.
Needless to say, we’re working on it and you can expect more BS from IoTSF.