And What Can We Do About It?
“Why is IoT Security so Hard and What Can We Do About It?” was the title of the talk by Dr. Nicholas Allott at the recent IoTSF Annual Conference. It was a very enlightening talk from the front line of IoT deployment and IoTSF asked Liam Baker to review the talk and tell us a little more about what peaked his interest. Over to you Liam:
 Allow me to introduce myself, I am a postgraduate student at the University of Warwick, in the field of Cyber Security Engineering. This profession peaked my interest in my undergraduate study and I began to focus on cryptocurrency, which is now the subject of my thesis. Dr Nicholas Allott of nquiringminds©, is featured in this first post, and this will cover all the key aspects of the opening presentation, curious? Let’s continue.
Allow me to introduce myself, I am a postgraduate student at the University of Warwick, in the field of Cyber Security Engineering. This profession peaked my interest in my undergraduate study and I began to focus on cryptocurrency, which is now the subject of my thesis. Dr Nicholas Allott of nquiringminds©, is featured in this first post, and this will cover all the key aspects of the opening presentation, curious? Let’s continue.
So, let’s begin by separating opinion from fact. Fact is that this is not an advertisement – or an excuse – for the purchase of that new Samsung kettle you have been deliberating over. However, I cannot guarantee as a review of an IoT security conference, hosted by the IoTSF, that there will be no opinion, all of which is heavily supported with experience and knowledge may I add.
That very same kitchen that perfects the boiling process, might also be indicative of how much time you spend at home, your social activity, perhaps even if you’re having a bad day or you’re ill. But most importantly, it may also be used as a gateway to eroding your privacy and stealing sensitive data. Some might argue that this is fear, personified.
From Smart Cities, Connected Cars, Industry 4.0 and Connected Health, Dr Allott, outlines the first problems of architecture and user experience being implemented at the expense of the capacity for the devices to be secure. Why is this? Memory in these devices is limited and the processing power to support cryptographic functionality is extremely poor. Dr Allott, points out that unified addressing (IPv4 and IPv6) is necessary but even a move to v6 will not solve any problems, and if you are using a combination of the aforementioned protocols? You are not really ‘doing’ IoT. What does this mean? Well, in essence, your IoT router which is your mobile application with zealous functionality, could be used a detonator for a lightbulb in your home. When we scale this to industry, the consequences become a little more tangible for safety.
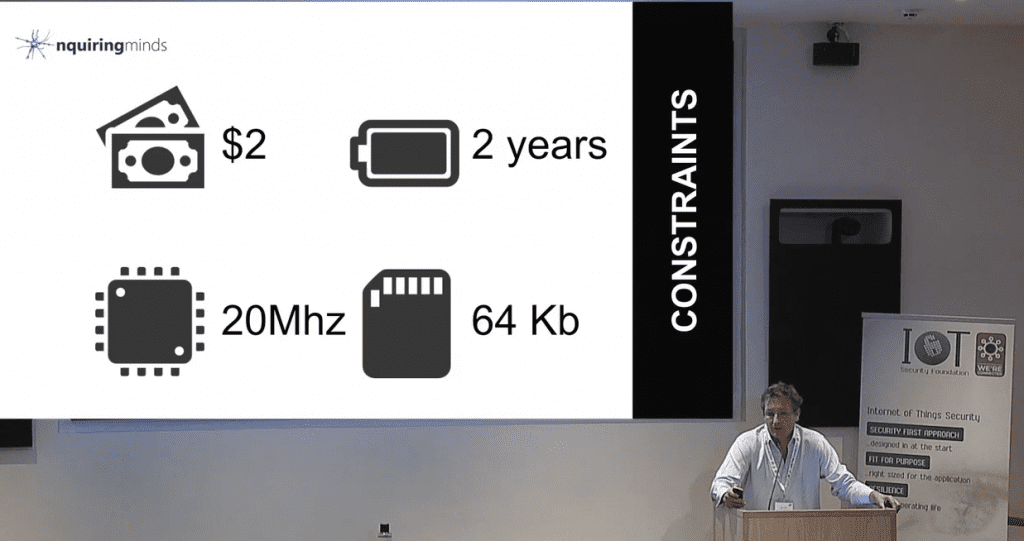
This problem is further characterised by Dr Allott as the ‘two dollar, two year’ use case, the expectancy of a device to last in the field two years after deployment is somewhat fantasy with the myriad of threat actors and sources and potentially reliant on vigilant user and the devices capacity for updating. So why is the transmission from router to device so fragile? With a 20Mhz processor and 64KB of RAM, you’d be forgiven for thinking $2 might have gotten you more for your money. This means that transmissions over a standard WPA2 network are unreliable, insecure and largely unsuitable for a device with such a small throughput. And while we’re being honest, the asymmetry and asynchronous nature of these networks isn’t helping us at all. The maths? Well this equates to 12 messages a day of uplink, with a maximum of 12 Bytes. Downlink is substantially worse with 2 messages being the threshold and of those the payload can be 8 Bytes. Queue looks of confusion and despair.
With a swarm of ubiquitous devices flooding the IoT battlefield, what provisioning system can we use for Device Identity is a question that Dr Allott approaches us with. Can your device handle session renegotiation and packet reassembly with that equating to 95% of your traffic? I think I can smell something burning. Now, if you thought that was an issue, there is currently a shortfall in the transparency of where the data origins are, where the data is going, and who it belongs to, bringing all sorts of authorisation problems to the forefront of this. Disclosure, it seems, has no boundaries in this reality. Dr Allott also briefly mentions the challenge of revocation, and if you want to know more about this, make sure you’re sitting comfortably and watch this particularly enlightening speech.
Worthy of noting, your root certificate, it controls you. You are seamlessly handing over all of the control you thought you had to that entity and possibly whoever controls it. This, is how the commercial ecosystem works. The router is the epicentre of all the secure connection that the device will make, cached data, relationships to devices (and device keys), endpoint for two secure connections and, you guessed it, physically insecure.
So one final note of this, hopefully light-hearted, initial overview of how not to disclose your darkest secrets (and TV channel you are watching from the smart meter you installed last month) are the key points. Your IoT device probably does not support encryption, is physically insecure bridging function is an attractive attack target and the local and remote management of devices provides even more challenges. As for the impact on your identity, the video will tell you more. Are there actually any solutions, Dr Allott covers them in the video, and covers them in great depth. Lastly, keep calm and do not become a foot soldier in a Botnet army.
Nick’s talk, and others, can be found here.